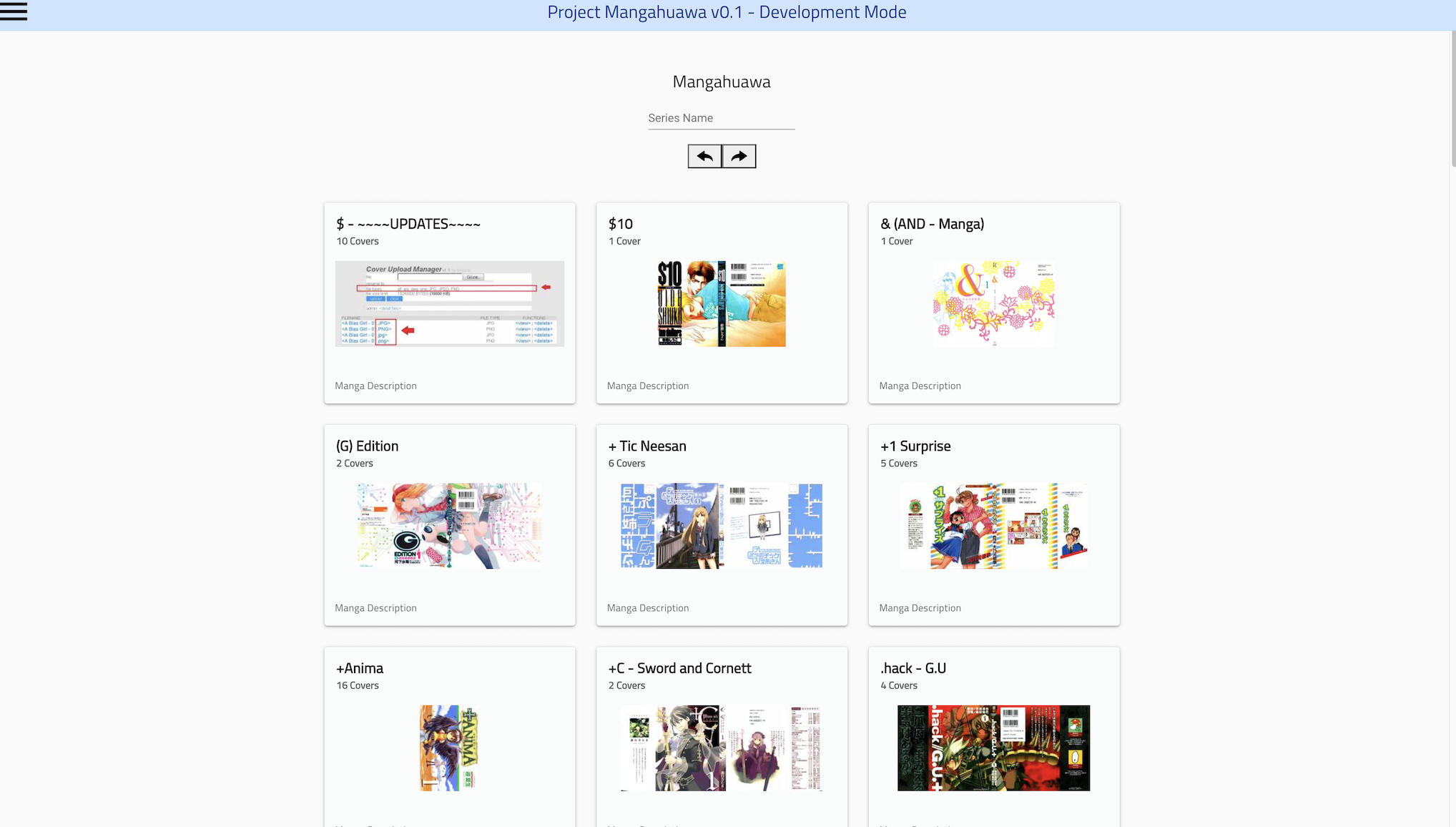
Project Mangahuawa
Nanatsu no Taizai - Soundtrack
|
UPDATES |
|
!!! Please Upload Covers
!!! |
|
If you have full covers for any of the missing
volumes, or you have covers for a manga,manhwa… that is not here on the site, please
upload them using the upload box below; (and please make sure the file name contains series name and volume number. |
|
To contact me, send an email to;
www@mokuton.com (You can also send your covers by email :p) |
At first glance, the filename kernel-dp-sneseur-release-v2.0.14-0-gd8b65c6.img looks like the output of a build script that escaped from a developer’s lab. It’s long, cryptic, and loaded with jargon. But to a firmware engineer, a reverse engineer, or a security researcher, this string is a treasure map.
The version v2.0.14 suggests that the device has already survived 14 patches. The question for a security team is: Were those patches feature additions, or were they CVEs? kernel-dp-sneseur-release-v2.0.14-0-gd8b65c6.img is not a random string. It is a concise history of a hardware platform, a snapshot of a development team’s discipline, and a warning sign to attackers. kernel-dp-sneseur-release-v2.0.14-0-gd8b65c6.img
Next time you see a long, ugly firmware filename, do not ignore it. Read it like a runestone. It has a story to tell. Want to analyze your own firmware? Start with binwalk kernel-dp-sneseur-release-v2.0.14-0-gd8b65c6.img to extract the filesystem, then strings to hunt for leaked secrets. The hash never lies. At first glance, the filename kernel-dp-sneseur-release-v2
While d8b65c6 is a short hash, it is enough to reconstruct the full commit if the attacker has access to a leak of the vendor’s repository or a public mirror. Once they have the source, they can search for vulnerabilities introduced in that specific commit. The version v2
"Sneseur" implies packet capture. If an attacker compromises this device, they know exactly what it is designed to do—likely mirror traffic or run deep packet inspection (DPI). This informs their lateral movement. They won’t waste time looking for a GPU; they will look for libpcap , tcpdump , or proprietary DPI rule files. 5. The Broader Trend: Deterministic Embedded Artifacts The most beautiful part of this filename is the 0-gd8b65c6 suffix. Five years ago, embedded firmware was often named final_firmware_v3_real_USE_THIS.bin . Chaos reigned.
For the engineer who built it, it is a job well done. For the reverse engineer who receives it, it is a starting point for a forensic journey. For the CISO who deploys it, it is a piece of the supply chain that must be tracked, patched, and defended.