Уже через 3 часа занятий вы сможете объясниться во время путешествия.
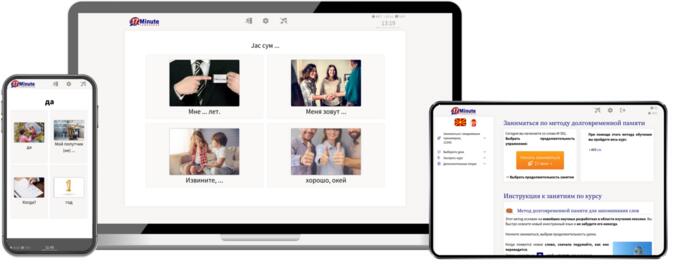
Программа работает на компьютере, смартфоне и планшете.
In the world of CNC machining, Predator Virtual CNC stands as a critical tool for simulation, verification, and optimization. It allows machinists and programmers to test G-code in a virtual environment before cutting metal, saving time and material.
However, the files associated with this software—including machine configurations, macros, and proprietary G-code programs—are valuable intellectual property. One common method for sharing or archiving these files is the ZIP format, and applying password protection is a key step in data security.
While it will not stop a determined attacker, it effectively prevents casual snooping, accidental exposure, and unauthorized forwarding of your valuable CNC programs and machine configurations.
For maximum security with Predator Virtual CNC, combine ZIP passwords with digital signatures or a secure managed file transfer (MFT) solution for your G-code distribution workflow. Disclaimer: Always comply with your organization’s IT security policies and export control regulations regarding CNC software and machine data.
In the world of CNC machining, Predator Virtual CNC stands as a critical tool for simulation, verification, and optimization. It allows machinists and programmers to test G-code in a virtual environment before cutting metal, saving time and material.
However, the files associated with this software—including machine configurations, macros, and proprietary G-code programs—are valuable intellectual property. One common method for sharing or archiving these files is the ZIP format, and applying password protection is a key step in data security.
While it will not stop a determined attacker, it effectively prevents casual snooping, accidental exposure, and unauthorized forwarding of your valuable CNC programs and machine configurations.
For maximum security with Predator Virtual CNC, combine ZIP passwords with digital signatures or a secure managed file transfer (MFT) solution for your G-code distribution workflow. Disclaimer: Always comply with your organization’s IT security policies and export control regulations regarding CNC software and machine data.
|
|
Рекомендуемое время занятий – всего 17 минут в день.
В любое время – в любом месте – на любом девайсе. |
|
|
Благодаря получившему множество наград методу обучения с использованием долговременной памяти вы никогда не забудете македонский.
|
|
|
При помощи новой технологии Superlearning вы сможете лучше заниматься и тратить на занятия на 32% меньше времени.
|
|
|
Изучение македонского еще никогда не было таким легким.
Какждый день вы получаете специально подобранные упражнения и учите иностранный язык автоматически. |
|
|
Разнообразные методы обучения гарантируют удовольствие и успех в учебе и мотивируют вас продолжать заниматься македонским каждый день.
|